Why Choose Us?
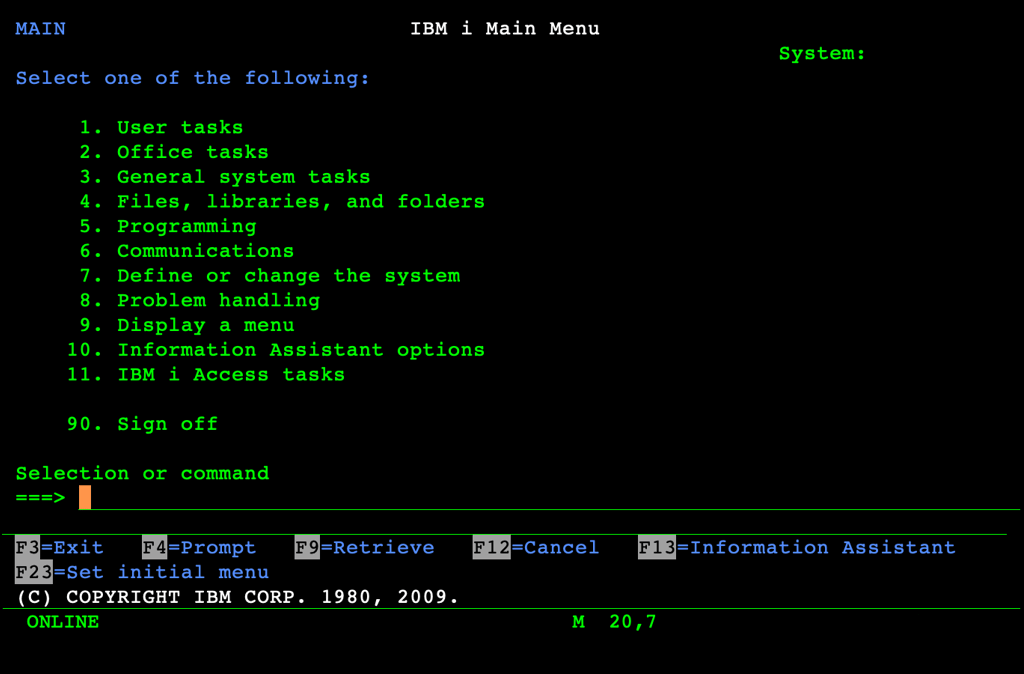
Organizations running legacy IBM i / AS400 environments face mounting operational, compliance, and modernization pressures — yet the expertise to navigate these challenges is scarce, and rapidly disappearing.
Many auditors do not understand legacy IBM i / AS400. Many technicians do not understand controls.
We understand both, through decades spent hands-on in both disciplines with highly regulated, global, US Public Companies.
Deep IBM i / AS400 Expertise
Work directly with a specialist who understands the platform’s architecture, risks, and operational realities. No guesswork. No hand-offs, No generic advice. Just precise, experience‑driven guidance from a single, accountable expert.
Governance, Risk & Compliance Insight
Weak controls, undocumented processes, and legacy access models create hidden exposure. Let us identify these blind spots, reduce audit risk, and help you establish a controlled, defensible environment.
Modernization With Clarity
Whether you’re planning a migration, preparing for a regulatory audit, or stabilizing a fragile environment, let us build a clear, actionable roadmap that aligns with your business priorities — not just technical theory.
Hands‑On, Not High‑Level
Get practical support, not just slide decks and salespeople. Let us work directly with your teams, your systems, and your real‑world constraints to deliver outcomes that hold up under scrutiny.
Future‑Ready Systems
Transform your undocumented, high‑risk environment into a controlled, compliant, and future‑ready system — giving you confidence in both day‑to‑day operations and long‑term strategy.
Lack of Ownership & Accountability - No defined owner for IBM i / AS400 security, operations, or compliance; decisions made informally by "those who know the system"
Impact: Controls degrade, risks go unaddressed, and no one is accountable for outcomes.Missing or Outdated Policies - Security, access, and change‑management policies are undocumented, outdated, or unenforced; legacy exceptions persist.
Impact: Compliance cannot be achieved with undocumented or inconsistent governance practices.
Insufficient Access Governance - User profiles, special authorities, and *PUBLIC access are not reviewed; segregation‑of‑duties conflicts go undetected; backdoor programs exist; programs run with elevated access regardless of the user's permissions.
Impact: Elevated risk of fraud, unauthorized changes, and regulatory non‑compliance.
Uncontrolled Change Management - Developers can move code into production without approval; no enforced change‑control process; emergency changes untracked.
Impact: Unapproved changes undermine system integrity, reliability and auditability.
Poor Data Governance - Sensitive data is not identified; access rules are unclear; changes to critical data are not logged or monitored.
Impact: Data integrity, confidentiality, and compliance obligations are compromised.
Lack of Monitoring & Reporting - High‑risk events do not generate alerts; logs are not reviewed; no dashboards for management oversight.
Impact: Governance requires visibility—you cannot improve what you cannot see.
Skills & Knowledge Gaps - Critical IBM i / AS400 knowledge resides with retiring staff; no succession planning or structured knowledge transfer.
Impact: Governance and business continuity risk increases when tribal knowledge walks out the door.
Weak Audit Readiness - Evidence cannot be produced; findings repeat; no structured remediation process.
Impact: Compliance risk and cost rises as audit confidence declines.
No Strategic Direction - No roadmap for modernization or risk reduction; decisions are reactive; risk posture is poorly understood.
Impact: The platform becomes a long‑term liability instead of a controlled asset.
Data Migration Project Management Risk - No migration strategy or governance; limited understanding of IBM i data and dependencies; insufficient expertise.
Impact: The organization becomes stranded on its legacy IBM i / AS400, unable to transition or modernize.